UNSEALED: WikiLeaks founder Julian Assange conspired with Manning to steal classified documents, prosecutors claim
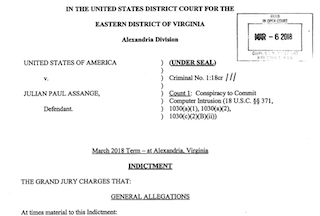
The United States District Court for the Eastern District of Virginia unsealed the indictment Monday against Wikileaks founder Julian Assange.
Before we get to the indictment let’s review excerpts from the Affidavit In Support of a Criminal Complaint and Arrest Warrant that was filed on December 21, 2017:
I, Megan Brown, make this affidavit in support of a criminal complaint charging the defendant, Julian P. Assange, with violating 18 U.S.C. §371 by conspiring to (1) access a computer, without authorization and exceeding authorized access, to obtain classified national defense information in violation of18 U.S.C. § 1030(a)(1); and (2) access a computer, without authorization and exceeding authorized access, to obtain information from a department or agency of the United States in furtherance of a criminal act in violation of18 U.S.C. §1030(a)(2), (c)(2)(B)(ii).

I am a Special Agent with the Federal Bureau of Investigation (FBI) and have been so employed since February 2011.
The facts in this Affidavit are based on my personal observations, information obtained from other agents and witnesses, my training and experience, and my review of records, reports, articles, and websites. Unless otherwise noted, information provided to me by other law enforcement personnel does not necessarily reflect my personal observations or investigation, but rather has been passed to me by individuals with first-hand knowledge. This Affidavit does not set forth all of my knowledge about this matter but is intended merely to establish probable cause for the criminal complaint.
As shown below, the conspirators took elaborate measures to conceal their communications, mask their identities, and destroy any trace of their conduct, using, for example, encryption and anonymization techniques, and erasing and wiping data. For this reason, the facts are derived in large part from forensic analysis of available computer data, remnants, or unalterable systems.
These charges relate to one of the largest compromises of classified information in the history of the United States. Between in or around January 2010 and May 2010, Chelsea Manning, an intelligence analyst in the U.S. Army, downloaded four, nearly complete and largely classified databases with approximately 90,000 Afghanistan war-related significant activity reports, 400,000 Iraq war-related significant activity reports, 800 Guantanamo Bay detainee assessments, and 250,000 U.S. State Department cables. Manning provided these records to WikiLeaks, a website founded and led by the defendant, Julian P. Assange. On its website, WikiLeaks expressly solicited classified information for public dissemination. WikiLeaks publicly released the vast majority of the classified records on its website in 2010 and 2011. Manning has since been tried and convicted by court-martial for her illegal acts in transmitting the information to WikiLeaks.

The charges in this criminal complaint focus on a specific illegal agreement that Assange and Manning reached in furtherance of Manning’s illegal disclosure of classified information. As explained below, investigators have recovered Internet “chats” between Assange and Manning from March 2010, The chats reflect that on March 8, 2010, Assange agreed to assist Manning in cracking a password stored on United States Department of Defense (DoD) computers connected to the classified Secret Internet Protocol Router Network (SIPRNet). Manning, who had access to the computers in connection with her duties as an intelligence analyst, was using the computers to download classified records to transmit to WikiLeaks.
Cracking the password would have allowed Manning to log onto the computers under a username that did not belong to her. Such a deceptive measure would have made it more difficult for investigators to determine the source of the illegal disclosures. While it remains unknown whether Manning and Assange were successful in cracking the password, a follow-up message from Assange to Manning on March 10, 2010, reflects that Assange was actively trying to crack the password pursuant to their agreement.
Circumstantial evidence reflects that Assange and Manning intended to crack the password to facilitate Manning’s illegal disclosure of classified information. At the time they formed their illegal password-cracking agreement, Manning had already provided WikiLeaks with hundreds of thousands of classified records relating to, among other things, the wars in Afghanistan and Iraq. In the recovered chats surrounding the illegal agreement. Manning and Assange engaged in real-time discussions regarding Manning’s transmission of classified records to Assange. The chats also reflect the two collaborating on the public release of the information and Assange actively encouraging Manning to provide more information. The chats, moreover, reflect that Manning actively took steps to try to conceal herself as the source of the leaks. Thus, the context of the agreement demonstrates that Assange and Manning intended to crack the password to facilitate Manning’s disclosure of classified information of the United States.

According to Manning, she began helping WikiLeaks soon after WikiLeaks publicly released messages from the September 11, 2001 terrorist attacks on November 25, 2009. As the examples in the following two sections demonstrate, Manning transmitted a large amount of classified information to WikiLeaks prior to March 2010, which was when she formed the agreement with Assange that is the subject of this complaint.
During her court-martial proceedings. Manning has admitted that, prior to March 2010, she provided WikiLeaks with classified significant activity reports from the Iraq and Afghanistan wars (“Iraq War Reports” and “Afghanistan War Reports,” respectively). According to Manning, she downloaded the Iraq War Reports and Afghanistan War Reports from the relevant CIDNE databases in late December 2009 and early January 2010, and initially saved the records on a CD-RW that she kept in her SCIF. Manning admitted that she later took the CD-RW out of the SCIF and copied the data from the CD-RW onto her personal laptop. Manning stated that she transferred the data from her laptop to a Secure Digital (“SD”) memory card, which she took with her when she went on leave later in January 2010.
Investigators later recovered the SD card that Manning used to transport the Iraq War Reports and Afghanistan War Reports. Forensic analysis of the SD card revealed that it contained the CIDNE databases for Iraq (391,883 records) and Afghanistan (91,911 records). The SD card also contained a README.txt file, which contained the following message:
Items of Historical Significance for Two Wars: Iraq and Afghanistan Significant Activities (SIGACTs) between 0000 on 01 JAN 2004 and 2359 on 31 DEC 2009 (Iraq local time, and Afghanistan local time) CSV extracts are from the Department of Defense (DoD) Combined Information and Data Exchange (CIDNE) Database. It’s already been sanitized of any source identifying information. You might need to sit on this information, perhaps 90-180 days, to figure out how best to release such a large amount of data, and to protect the source. This is possibly one of the more significant documents of our time, removing the fog of war, and revealing the true nature of21st century asymmetric warfare. Have a good day.
According to Manning, she uploaded the Iraq War Reports, Afghanistan War Reports, and README.txt file to the WikiLeaks website on or around February 3, 2010. WikiLeaks publicly released the Iraq War Reports and Afghanistan War Reports on its website later in 2010. In July 2010, WikiLeaks released approximately 76,000 of the Afghanistan War Reports. Then, in October 2010, WikiLeaks released approximately 391,832 Iraq War Reports.
Manning and WikiLeaks had reason to believe that public disclosure of the Afghanistan War Reports and Iraq War Reports would cause injury to the United States. Documents included in the Afghanistan War Reports contained information the disclosure of which potentially endangered U.S. troops and Afghan civilians, and aiding enemies of the United States. Numerous Secret reports, for example, related to the identity and significance of local supporters of the United States and Coalition forces in Iraq and Afghanistan.
In fact, according to July 30, 2010, New York Times article “Taliban Study WikiLeaks to Hunt Informants,” after the release of the Afghanistan War Reports, a member of the Taliban contacted the New York Times and stated, “We are studying the report. We knew about the spies and people who collaborate with U.S. forces. We will investigate through our own secret service whether the people mentioned are really spies working for the U.S. If they are U.S. spies, then we will know how to punish them.”
Moreover, on May 2, 2011, United States government officials raided the compound of Usama bin Laden in Abbottabad, Pakistan. During the raid, they collected a number of items of digital media, which included, among other things, (1) a letter from bin Laden to another member of the terrorist organization al-Qaeda in which bin Laden requested that the member gather the DoD material posted to WikiLeaks, and (2) a letter from that member of al-Qaeda to Bin Laden with information from the Afghanistan War Reports released by WikiLeaks.
In addition, some of the Afghanistan War Reports included detailed reports of improvised explosive device (“lED”) attacks on the United States and Coalition forces in Afghanistan. The enemy could use these reports to plan future lED attacks because they described lED techniques, devices, and explosives, and revealed the countermeasures used by the United States and Coalition forces against lED attacks and potential limitations to those countermeasures.
I have reviewed a number of the Afghanistan War Reports and Iraq War Reports that WikiLeaks released. The reports that I reviewed contained classification markings reflecting that they were classified as “SECRET.” This suggests that the versions of the Afghanistan Reports and Iraq War Reports that Manning transmitted to WikiLeaks clearly reflected that they were classified.
Agreement To Crack Password
On March 8, 2010, at approximately 3:55 p.m., Manning asked Assange whether he was “any good at Im hash cracking.”
At the time, Windows operating systems commonly used two methods for hashing and storing passwords, Lan Manager (LM) and New Technology Lan Manager (NTLM). Referring to an LM hash or an NTLM hash is tantamount to saying, “Windows password.” Thus, in the above-described message, Manning asked Assange if he was able to crack passwords for computers running Windows operating systems. In response to Manning’s question, Assange answered, “yes.” Assange then stated, “we have rainbow tables for Im.” A “rainbow table” is a tool used to crack a hash value to determine the password associated with it. After Assange claimed to have rainbow tables, Manning stated “lc.” Manning then stated, “I think its Im +Imnt.”
Manning likely meant to say “Im + ntlm.” The hexadecimal string of text is consistent with the format of an LM or NTLM hash. Further, on Windows operating system version Vista or newer, LM is disabled, and only NTLM is used. Manning’s remark that she “thought” that the hash was “Im + Imnt” suggests that she retrieved it from a computer running a pre-Vista version of Windows. A few minutes later, Manning further explained, “not even sure if that’s the hash…. I had to hex dump a SAM file since I don’t have the system file.” Assange asked, “what makes you think [it’s]Im?” Assange asked, “it’s from a SAM?” Manning answered “yeah.” Assange then stated that he “passed it onto our Im guy.”
In the above-described chats, Manning informed Assange that she had accessed the SAM file with a program and had identified this particular 16-byte hexadecimal value as a potential LM or NTLM password hash. By saying she retrieved the password hash through a “hex dump,” Manning likely meant that she used a software program to view the SAM file in “hexadecimal format,” in which raw computer data can be viewed.
Two days later, at approximately 11:30 p.m. on March 10, 2010, Assange followed up on the issue. Assange messaged Manning and asked, “any more hints about this Im hash?” Assange stated, “no luck so far.” Investigators have not recovered a response by Manning to Assange’s question, and there is no other evidence as to what Assange did, if anything, with respect to the password. The next chats that investigators were able to recover were dated March 16, 2010. Thus, there is approximately a six-day gap in the chats after Assange asked for further hints on the hash. Nevertheless, the recovered chats described above reflect an agreement between Manning and Assange to crack the hash.
The evidence summarized in this Affidavit establishes probable cause to believe that the defendant, Julian P. Assange, committed the offense alleged in the complaint; namely, Assange violated 18 U.S.C. § 371 by conspiring to (1) access a computer, without authorization and exceeding authorized access, to obtain classified national defense information in violation of 18 U.S.C. § 1030(a)(1); and (2) access a computer, without authorization and exceeding authorized access, to obtain information from a department or agency of the United States in furtherance of a criminal act in violation of18 U.S.C. § 1030(a)(2), (c)(2)(B)(ii).
Respectfully submitted, Special Agent Megan Brown Federal Bureau of Investigation.

Excerpts from the Indictment against Julian Assange
Julian Paul Assange was the founder and leader of the WikiLeaks website. The WikiLeaks website publicly solicited submissions of classified, censored, and other restricted information. Assange, who did not possess a security clearance or need to know, was not authorized to receive classified information of the United States.
Between in or around January 2010 and May 2010, Manning downloaded four, nearly complete databases from departments and agencies of the United States. These databases contained approximately 90,000 Afghanistan war-related significant activity reports, 400,000 Iraq war-related significant activities reports, 800 Guantanamo Bay detainee assessment briefs, and 250,000 U.S. Department of State cables. Many of these records were classified pursuant to Executive Order No. 13526or its predecessor orders. Manning provided the records to agents of WikiLeaks so that WikiLeaks could publicly disclose them on its website. WikiLeaks publicly released the vast majority of the classified records on its website in 2010and 2011.
On or about March 8, 2010, Assange agreed to assist Manning in cracking a password stored on United States Department of Defense computers connected to the Secret Internet Protocol Network, a United States government network used for classified documents and communications, as designated according to Executive Order No. 13526 or its predecessor orders.
Manning, who had access to the computers in connection with her duties as an intelligence analyst, was also using the computers to download classified records to transmit to WikiLeaks. Army regulations prohibited Manning from attempting to bypass or circumvent security mechanisms on Government-provided information systems and from sharing personal accounts and authenticators, such as passwords.
The portion of the password Manning gave to Assange to crack was stored as a “hash value” in a computer file that was accessible only by users with administrative-level privileges. Manning did not have administrative-level privileges and used special software, namely a Linux operating system, to access the computer file and obtain the portion of the password provided to Assange.
Cracking the password would have allowed Manning to log onto the computers under a username that did not belong to her. Such a measure would have made it more difficult for investigators to identify Manning as the source of disclosures of classified information.
Prior to the information of the password-cracking agreement, Manning had already provided WikiLeaks with hundreds of thousands of classified records that she downloaded from departments and agencies of the United States, including the Afghanistan war-related significant activity reports and Iraq war-related significant activities reports.
At the time he entered into this agreement, Assange knew that Manning was providing WikiLeaks with classified records containing national defense information of the United States. Assange was knowingly receiving such classified records from Manning for the purpose of publicly disclosing them on the WikiLeaks website.
For example, on March 7, 2010, Manning and Assange discussed the value of the Guantanamo Bay detainee assessment briefs, and on March 8, 2010, before entering the password cracking-agreement. Manning told Assange that she was “throwing everything [she had] on JTF GTMO at [Assange] now.” Manning also said, “after this upload, that’s all I really have got left.” To which Assange replied, “curious eyes never run dry in my experience.” Following this, between March 28, 2010, and April 9, 2010, Manning used a United States Department of Defense computer to download the U.S. Department of State cables that WikiLeaks later released publicly.
COUNT ONE
The general allegations set forth in paragraphs 1 through 13 are re-alleged and incorporated into this Count as though fully set forth herein. Beginning on or about March 2, 2010, and continuing thereafter until on or about March 10, 2010, the exact date being unknown to the Grand Jury, both dates being approximate and inclusive, in an offense begun and committed outside of the jurisdiction of any particular State or district of the United States, the defendant, JULIAN PAUL ASSANGE, who will be first brought to the Eastern District of Virginia, did knowingly and intentionally combine, conspire, confederate and agree with other co-conspirators known and unknown to the Grand Jury to commit an offense against the United States, to wit:
(A) to knowingly access a computer, without authorization and exceeding authorized access, to obtain information that has been determined by the United States Government pursuant to an Executive order and statute to require protection against unauthorized disclosure for reasons of national defense and foreign relations, namely, documents relating to the national defense classified up to the “Secret” level, with reason to believe that such information so obtained could be used to the injury of the United States and the advantage of any foreign nation, and to willfully communicate, deliver, transmit, and cause to be communicated, delivered, or transmitted the same, to any person not entitled to receive it, and willfully retain the same and fail to deliver it to the officer or employee entitled to receive it; and
(B) to intentionally access a computer, without authorization and exceeding authorized access, to obtain information from a department and agency of the United States in furtherance of a criminal act in violation of the laws of the United States, that is, a violation of Title 18, United States Code, Sections 641, 793(c), and 793(e). (In violation of Title 18, United States Code, Sections 371,1030(a)(1), 1030(a)(2), 1030(c)(2)(B)(ii).)
PURPOSE AND OBJECT OF THE CONSPIRACY
- The primary purpose of the conspiracy was to facilitate Manning’s acquisition and transmission of classified information related to the national defense of the United States so that WikiLeaks could publicly disseminate the information on its website.
MANNERS AND MEANS OF THE CONSPIRACY
Assange and his co-conspirators used the following ways, manners and means, among others, to carry out this purpose:
It was part of the conspiracy that Assange and Manning used the “Jabber” online chat service to collaborate on the acquisition and dissemination of the classified records, and to enter into the agreement to crack the password stored on United States Department of Defense computers connected to the Secret Internet Protocol Network.
It was part of the conspiracy that Assange and Manning took measures to conceal Manning as the source of the disclosure of classified records to WikiLeaks, including by removing usernames from the disclosed information and deleting chat logs between Assange and Manning.
It was part of the conspiracy that Assange encouraged Manning to provide information and records from departments and agencies of the United States.
It was part of the conspiracy that Assange and Manning used a special folder on a
Cloud drop box of WikiLeaks to transmit classified records containing information related to the national defense of the United States.
ACTS IN FURTHERANCE OF THE CONSPIRACY
In order to further the goals and purposes of the conspiracy, Assange and his co-conspirators committed overt acts, including, but not limited to, the following:
On or about March 2, 2010, Manning copied a Linux operating system to a CD, to allow Manning to access a United States Department of Defense computer file that was accessible only to users with administrative-level privileges.
On or about March 8, 2010, Manning provided Assange with part of a password stored on United States Department of Defense computers connected to the Secret Internet Protocol Network.
On or about March 10, 2010, Assange requested more information from Manning related to the password. Assange indicated that he had been trying to crack the password by stating that he had “no luck so far.”
Is Julian Assange just a publisher of leaked materials or worse
Whistleblowers throughout the decades have leaked confidential information to news organizations, which have published the documents based on the First Amendment of the Constitution which protects freedom of the press. The Pentagon Papers was one such example.
The question here though according to what the government alleges against Assange, is that he not only received classified government documents but that Assange crossed over the line by assisting Chelsea Manning in attempting to break a password to access government databases and thus involved himself in a criminal conspiracy. (President Obama pardoned Manning, who was facing 35 years in prison.)
That will have to be proven in a court of law, however, ramifications that this case could have on freedom of the press is mind-boggling.
If a journalist meets secretly with a whistleblower to protect the identity of the person giving them the information, can a case be made against the journalist for conspiring with the source to protect their identity?
When does a journalist/publisher cross over the line to criminal activity?
If someone wants to give me information that is one thing. If I have to assist them by breaking into a building or a computer so the information can be accessed, I would say I just became involved in criminal activity. Freedom of the press would not protect me in that case.
President Donald Trump praised Wikileaks during his campaign in 2016, telling supporters he loves what Assange did. Fast forward to 2019, Trump now says he knows nothing about WikiLeaks. How that will impact the case against Julian Assange remains to be seen.

Doug authored over 135 articles on the October 1, 2017, Las Vegas Massacre, more than any other single journalist in the country. He investigates stories on corruption, law enforcement, and crime. Doug is a US Army Military Police Veteran, former police officer, deputy sheriff, and criminal investigator. Doug spent 20 years in the hotel/casino industry as an investigator and then as Director of Security and Surveillance. He also spent a short time with the US Dept. of Homeland Security, Transportation Security Administration. In 1986 Doug was awarded Criminal Investigator of the Year by the Loudoun County Sheriff’s Office in Virginia for his undercover work in narcotics enforcement. In 1991 and 1992 Doug testified in court that a sheriff’s office official and the county prosecutor withheld exculpatory evidence during the 1988 trial of a man accused of the attempted murder of his wife. Doug’s testimony led to a judge’s decision to order the release of the man from prison in 1992 and awarded him a new trial, in which he was later acquitted. As a result of Doug breaking the police “blue wall of silence,” he was fired by the county sheriff. His story was featured on Inside Edition, Current Affair and CBS News’ “Street Stories with Ed Bradley”. In 1992 after losing his job, at the request of the Federal Bureau of Investigation, Doug infiltrated a group of men who were plotting the kidnapping of a Dupont fortune heir and his wife. Doug has been a guest on national television and radio programs speaking on the stories he now writes as an investigative journalist. Catch Doug’s Podcast: @dougpoppa1
1.) They have and cannot provide that it was Assange and Assange alone that Manning was chatting with on Jabber because it was Jabber.
2.) If a source comes to me and asks can you get the safe password and I say, “Sure, I’ll get my safecrackers on it.” then the next day I say, “Sorry, no luck. Did you get more docs for me?” You would have to prove I did go to a safecracker and was not just lying to coddle the source. In other words, they have to show intent.
All that said, the charges are not as important as the extradition. The extradition needs to be fought and pushed back against tooth and nail because once they get him here they will throw many more charges on top of this lame duck charge.